In today’s digital age, online security is paramount for individuals and businesses alike. With the increasing number of cyber threats and data breaches, safeguarding personal information has become more important than ever. One effective method to enhance online security is through the implementation of two-factor authentication (2FA).
This article will delve into the importance of 2FA, its benefits, and how it can significantly protect your online data. Whether you are an individual concerned about your personal information or a business looking to protect your brand reputation, understanding the significance of 2FA is crucial.
Understanding the risks of online security
Cyber threats and data breaches have become a common occurrence in today’s digital landscape. Hackers leverage various attack vectors to gain unauthorized access to personal and business accounts, putting sensitive information at risk. Understanding the potential risks is crucial to appreciate the importance of two-factor authentication (2FA) in enhancing online security.
One of the primary risks is password theft. Cybercriminals employ sophisticated techniques like phishing, malware, and brute force attacks to obtain login credentials. With a simple username and password, they can easily compromise your online accounts, leading to severe consequences.
Another significant risk is account takeovers. Once hackers gain access to your account, they can impersonate you, carry out unauthorized transactions, or manipulate your information for their malicious intent. The ramifications of such activities can be devastating, resulting in financial loss, reputational damage, and even legal issues.
These risks highlight the urgency to implement additional security measures, such as 2FA. By requiring an additional step in the authentication process, usually a temporary code sent to your registered device, 2FA provides an extra layer of protection against unauthorized access. This method acts as a second barrier, making it significantly more difficult for hackers to breach your accounts.
In the next section, we will explore the benefits of two-factor authentication and how it addresses the risks mentioned above. Stay tuned to discover how this simple yet effective security measure can enhance your online security and provide you with peace of mind.
What is two-factor authentication?
Two-factor authentication (2FA) is a security measure that adds an extra layer of protection to your online accounts. It requires users to provide two pieces of identifying information to verify their identity, making it significantly more difficult for hackers to gain unauthorized access.
The first factor is usually something you know, such as a password or a PIN. This is the initial barrier to entry and acts as the first level of security. However, as mentioned earlier, relying solely on passwords can be risky due to the increasing sophistication of cyberattacks.
The second factor is typically something you have, such as a physical token or a one-time temporary code sent to your registered device. This additional step ensures that even if your password is compromised, unauthorized access is still prevented as the hacker would require physical possession of the second factor.
By implementing two-factor authentication, you create an extra level of security that significantly reduces the risk of password theft and account takeovers. In the next section, we will delve into the specific benefits of using 2FA and how it can enhance your online security.
The advantages of implementing two-factor authentication
Now that we understand the basics of two-factor authentication (2FA), let’s explore the specific benefits it brings to enhance your online security.
First and foremost, 2FA provides an additional layer of protection against unauthorized access. With just a password, hackers can easily infiltrate your accounts if they manage to crack or obtain it. However, by requiring a second factor, such as a physical token or a one-time temporary code, even if your password gets compromised, the chances of an attacker gaining access to your accounts are significantly reduced.
Setting up 2FA is a straightforward process that can be done for various online platforms, avoid using apps that won’t let you export your keys easily, and please don’t use any google services,
Instead use:
Aegis: A free, secure and open source app for Android to manage your 2-step verification tokens. Supports variety of imports from other apps (Google Authenticator, Authy etc.), vault encryption and exporting keys (plaintext or encrypted).
ente Auth: A free, cross platform, end-to-end encrypted and open source app for managing your 2-step verification tokens. From the makers of ente Photos, and uses the same battle tested infrastructure. Needs an ente.io account.
Owky: Free and Open Source Two-Factor Authenticator for IOS users.
FreeOTPPlus: Enhanced fork of FreeOTP-Android providing a feature-rich 2FA authenticator.
RaivoOTP: A native, lightweight and secure one-time-password (OTP) solution for iOS users.
Authenticator Pro: – A Two-Factor Authentication (2FA) client designed for Android and Wear OS.
Whichever method you choose, make sure to follow the provided instructions carefully to properly set up and configure two-factor authentication for your account.
In the following section, we will delve deeper into the benefits and considerations of each authentication method, helping you make an informed decision regarding which method is most suitable for your needs.
Additional measures to enhance your online security
While two-factor authentication (2FA) is an effective method for enhancing online security, it is important to remember that it is just one piece of the puzzle. There are additional measures you can take to further protect your online accounts and information.
1. Strong and Unique Passwords: Ensure that you create strong and unique passwords for each of your online accounts. Avoid reusing passwords and consider using a password manager to generate and store complex passwords securely.
2. Regularly Update Software: Keeping your operating system, software, and applications up to date is crucial. Updates often include security patches that address vulnerabilities, reducing the risk of exploitation.
3. Be Wary of Phishing Attempts: Be vigilant when it comes to suspicious emails or messages asking for personal information. Avoid clicking on unfamiliar links and always verify the sender’s identity before providing any sensitive data.
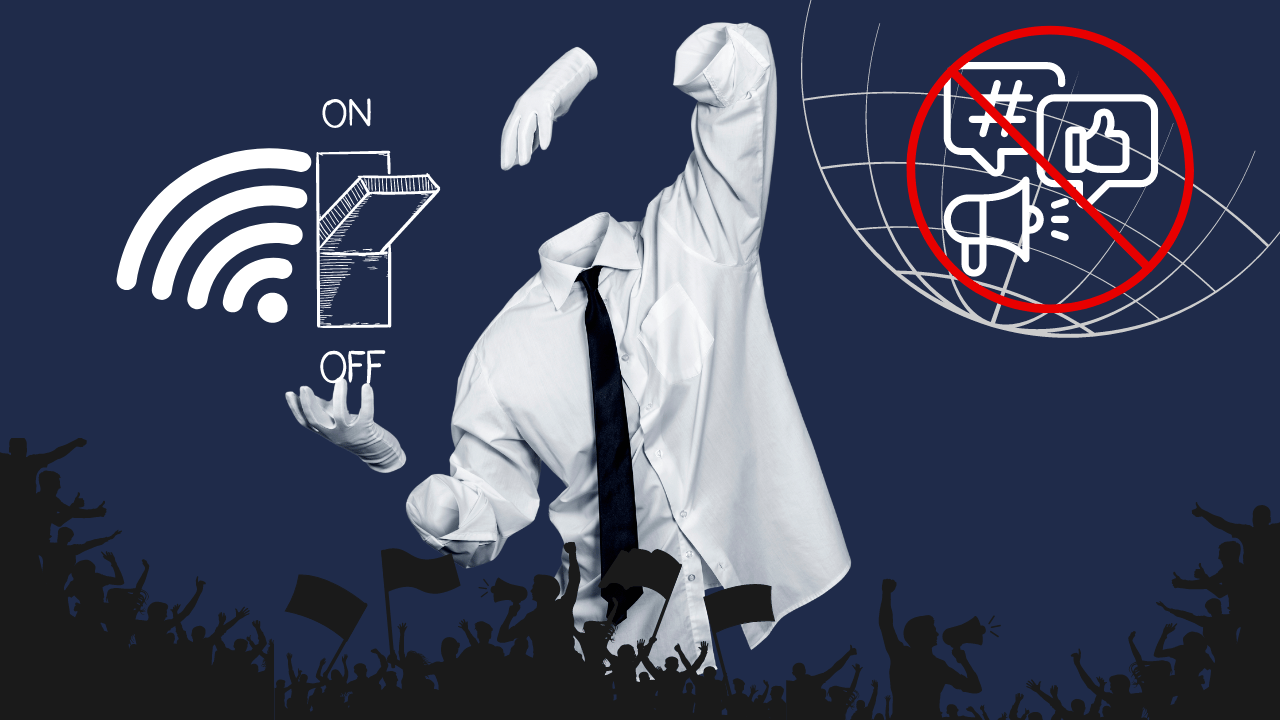
4. Secure Wi-Fi Networks: When accessing the internet, make sure you are using a secure, encrypted Wi-Fi network. Avoid connecting to public or unsecured networks, as they can leave your data vulnerable to interception.
5. Monitor Account Activity: Regularly review your online account activity and enable any available account alerts. This will help you spot any unauthorized access or suspicious behavior promptly.
By implementing these additional measures alongside two-factor authentication, you can greatly enhance your online security and better protect your sensitive information. Stay tuned for the next section, where we will discuss the importance of regularly updating and reviewing your security settings.